Your Security Scanner Just Attacked You
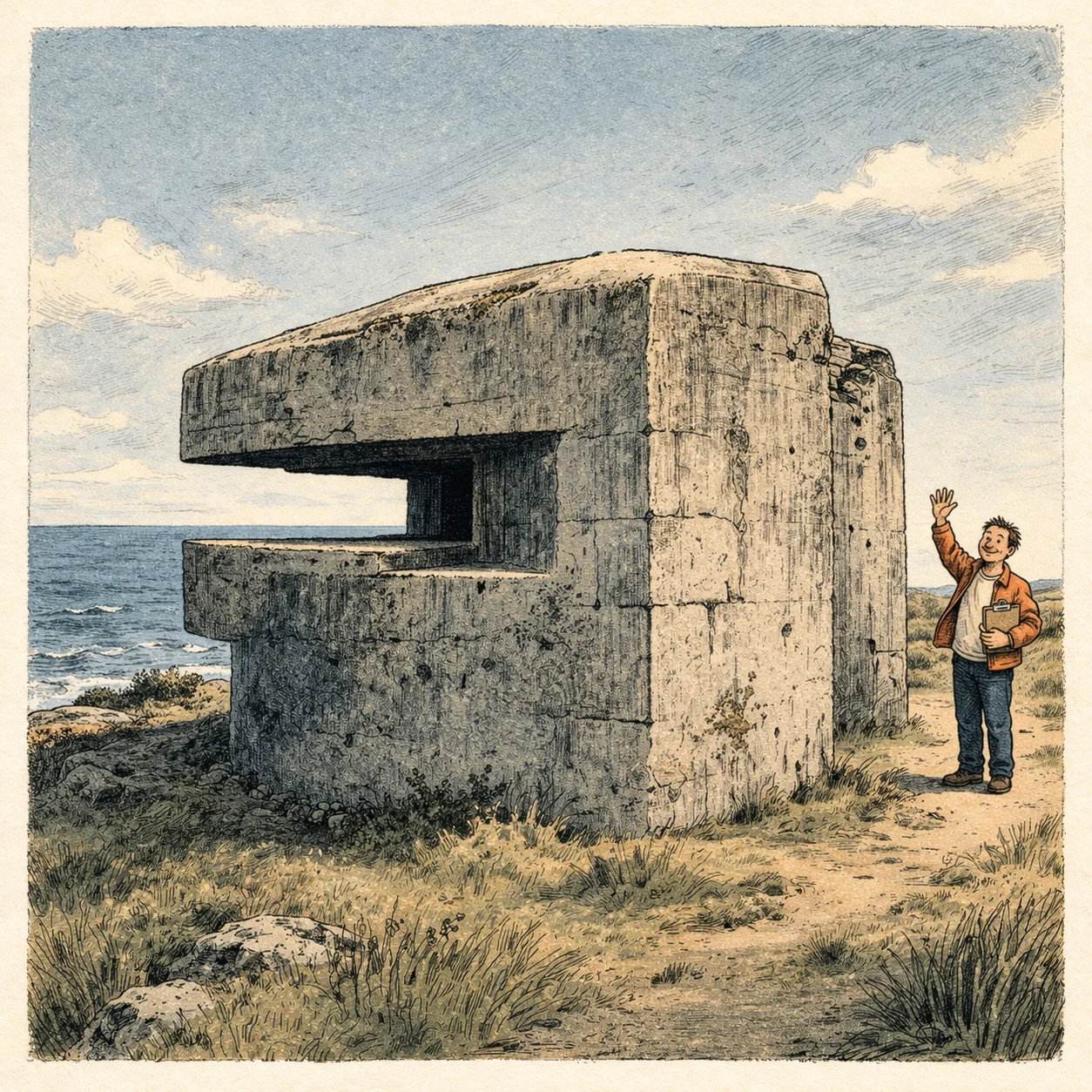
Two centuries ago, the Austrians fortified the city of Ulm and waited for Napoleon to attack. He didn't. He went around them, cut them off from behind, and 60,000 soldiers surrendered without the defences ever being tested.
This kept happening. Before World War II, France built the Maginot Line along the German border, the most expensive defensive fortification in history. Germany just drove around the end of it and France fell in six weeks. The Germans then built their own version, the Atlantic Wall, to stop an Allied invasion. All five Normandy beaches were in Allied hands by nightfall on D-Day. In 1973, Israel's Bar Lev Line along the Suez Canal was considered impenetrable. Egypt broke through it within hours.
This isn't to take anything away from the people who defended these lines. If you want to read stories of extraordinary endurance, you'll find them in these histories. But they were fighting for a flawed strategy. Most of these fortifications didn't collapse. They didn't need to. They were made irrelevant, because their enemy could move and they could not.
That's the pattern. Static perimeter defences fail not because the walls are weak, but because they're predictable and they assume the enemy will attack where they're strongest.
For a long time, most organisations repeated this pattern with their cyber strategies. Many still do. But that's starting to change, motivated by incidents like the recent Trivy supply chain compromise.
Trivy
A few weeks ago, attackers compromised Trivy, one of the most widely used open-source security scanners, through a GitHub misconfiguration. They backdoored the scanner and used credentials stolen from compromised pipelines to expand into further tools, including Checkmarx and LiteLLM. Payloads were then distributed via these compromised tools that harvested cloud credentials, API tokens, SSH keys and Kubernetes secrets from over a thousand enterprise environments.
No firewall stopped it. No email gateway caught it. No EDR flagged it. The threat arrived through trusted software, running inside build pipelines, with the credentials those organisations had given it.
The Trivy compromise is a supply chain attack, and it'll be analysed as one. But there's a simpler lesson underlying it: if all your defences face outward, an attack that starts on the inside has nothing to fight.
Mandiant's M-Trends 2025 report puts the global median dwell time at 11 days, meaning attackers are sitting inside networks for nearly two weeks before anyone notices. And the breakout time? CrowdStrike data shows the average time from initial access to first lateral movement is 62 minutes. One hour. That's how long you have before an attacker starts moving through your network. If there's nothing watching the hallways, no internal detection, no deception, no segmentation creating chokepoints...well, we've seen how history treats those who focus too heavily on defending the perimeter.
The gap
Ask any CISO whether they believe in defence-in-depth. They'll say yes. Of course. It's been security orthodoxy for decades. Next, ask to see their budget.
For years there's been a gap between what organisations say they believe and where they actually put their money. The SANS 2025 Detection & Response Survey shows the scale of it: twenty-eight percent of organisations describe their detection and response budget as outright insufficient. Only a quarter say it's actually adequate. And 47% rank budget constraints as the single biggest obstacle to maintaining effective detection and response.
But the real gap is deeper than that: even the detection and response spending that exists has mostly been pointed at the perimeter. SaaS-based EDR on endpoints. Network monitoring focused on inbound and outbound traffic. A SIEM ingesting firewall and proxy logs. That's cyber defence for sure. But it's defence of the front door. It's watching who comes in and out.
That's not defence-in-depth. That's a taller wall.
We should be clear about definitions here, because these terms gets used and misused a lot. When we talk about defence, we aren't talking about patching systems, enforcing MFA or awareness training. These things are absolutely necessary, but they aren't defence. Defence means having the capability to find and stop attackers. And defence-in-depth means that capability exists throughout your environment, not just at the boundary but in the core. The messy middle of the kill chain that gets less attention because it's so hard.
If you're still telling the board the wall is enough, the Trivy attack and the ones that will follow it should give you pause. The question isn't whether someone will get past your perimeter. That's already been answered. The question is what happens when they do.
Data sources: SANS 2025 Detection & Response Survey; Mandiant M-Trends 2025; CrowdStrike threat intelligence. Breach details sourced from public incident reporting including Microsoft, CrowdStrike, and Aqua Security advisories on the Trivy/LiteLLM supply chain compromise.